Adguard VPN is a commercial VPN solution, but the company has decided to open-source the VPN protocol and named it TrustTunnel. It’s described as a modern, secure, mobile-optimized VPN protocol.
Since there are plenty of VPN protocols, including WireGuard and OpenVPN, it felt redundant at first. But AdGuard explains that those are easy to detect and block at the network level, and methods to conceal VPN traffic, such as wrapping VPN data in a TCP connection, often reduce speed.
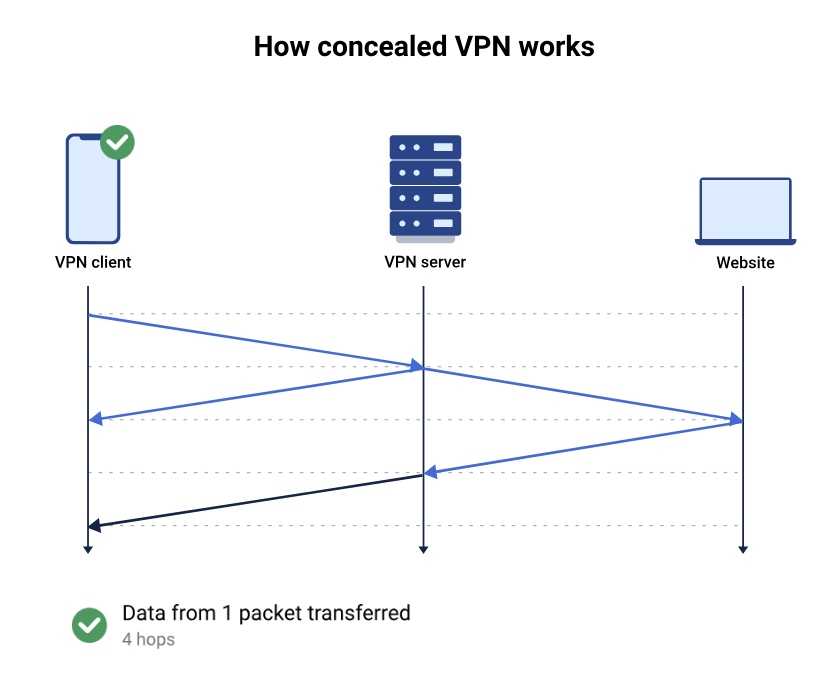
Concealed VPN with four hops per packet
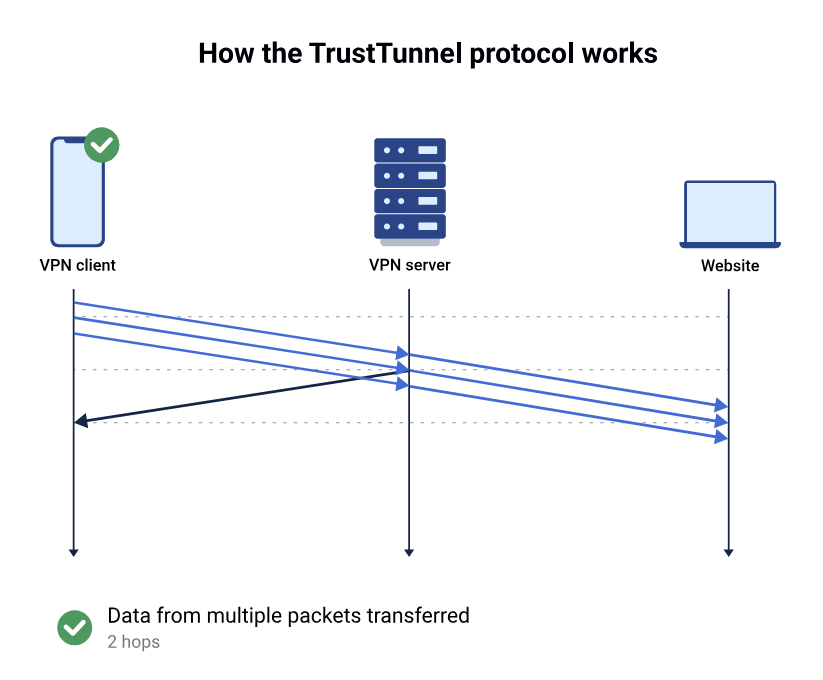
TrustTunnel relies on a different method and blends in with regular HTTPS traffic through TLS-based encryption, and HTTP/2 or HTTP/3 transport. Each connection runs on its own dedicated stream, which combines packets for more efficient transmission. The diagrams above and below illustrate this by showing that four hops are required for a standard concealed VPN, and only two hops with TrustTunnel. The company also says it is optimized for mobile platforms and performs well even in unstable network conditions.
TrustTunnel is completely independent from AdGuard VPN, and the company released the complete code of its reference implementation of the TrustTunnel server and its clients under a permissive Apache 3.0 license. You’ll find three repositories on GitHub:
“TrustTunnel” – VPN protocol written in Rust
“TrustTunnelClient” – Command-line client mostly written in C++ for Linux, Windows, and macOS
“TrustTunnelFlutterClient” – A Flutter client for Android and iOS, mostly written in Dart; You can also install the apps directly from Google Play or the Apple App Store.
AdGuard explain the clients currently allow the users to:
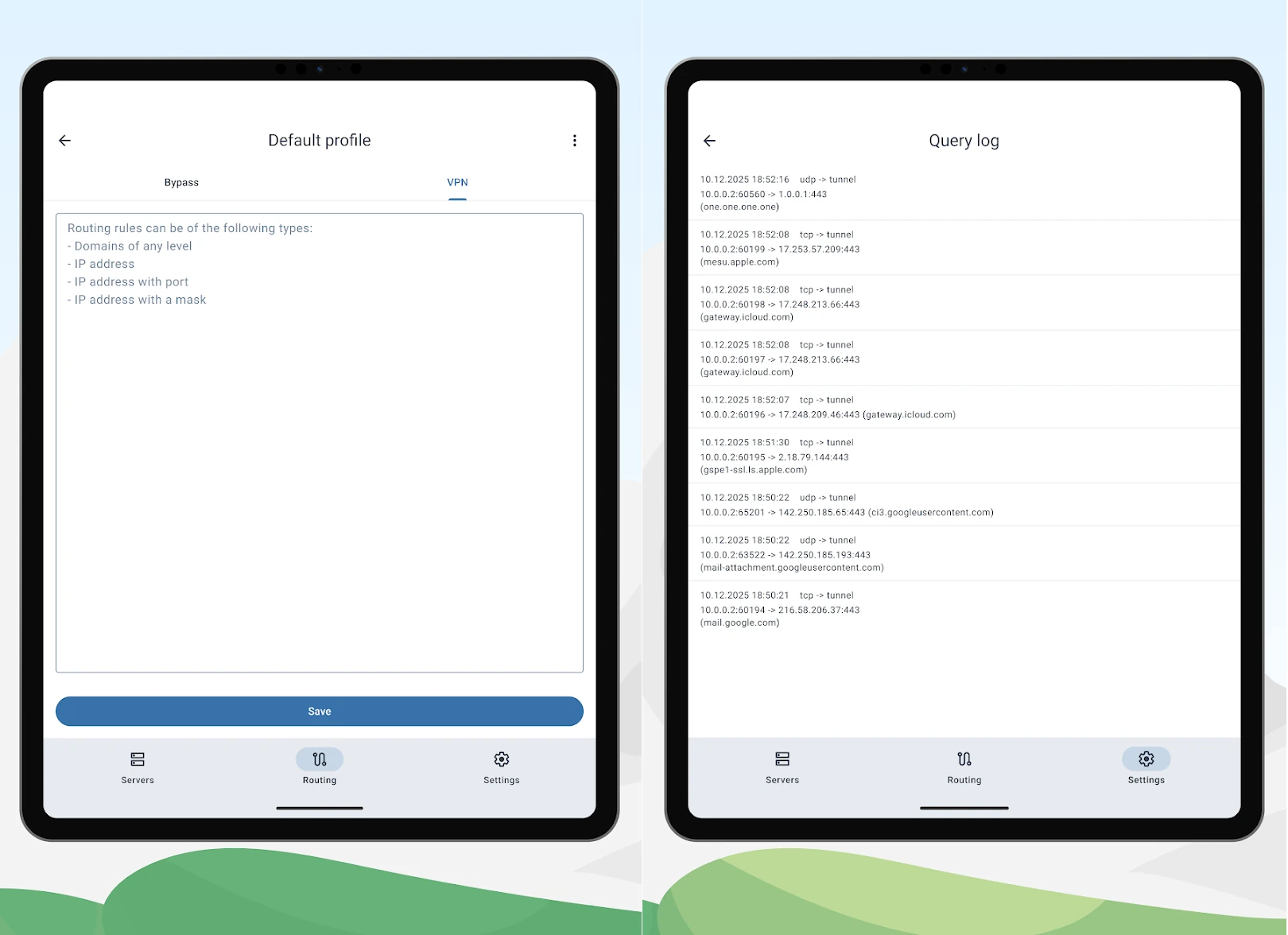
Use flexible routing rules to decide which requests go through the tunnel and which stay on the local network
Exercise fine-grained control, separating work and personal traffic, routing specific domains or apps, and tuning network behavior
Benefit from a real-time request log that provides full transparency into where the device sends traffic, how routing rules apply, and which connections use the tunnel
From what I understand, the main benefit of TrustTunnel is to avoid being detected/blocked while keeping better performance than concealed VPN through WireGuard or other solutions. If blocking/detection is not an issue, WireGuard will probably still be preferred since it should deliver excellent performance when no obfuscation/concealment is needed, and its low code footprint makes it more suitable for resource-constrained devices, and there’s even an ESP32 WireGuard implementation.
TrustTunnel relies on HTTPS, requiring more resources and is likely unsuitable for most microcontrollers. However, it might end up in routers as a VPN option along with WireGuard and OpenVPN.
You’ll find more details in the announcement and the project’s website.
Thanks to TLS for the tip.
Source: CNX Software
Author: Jean-Luc Aufranc (CNXSoft)
